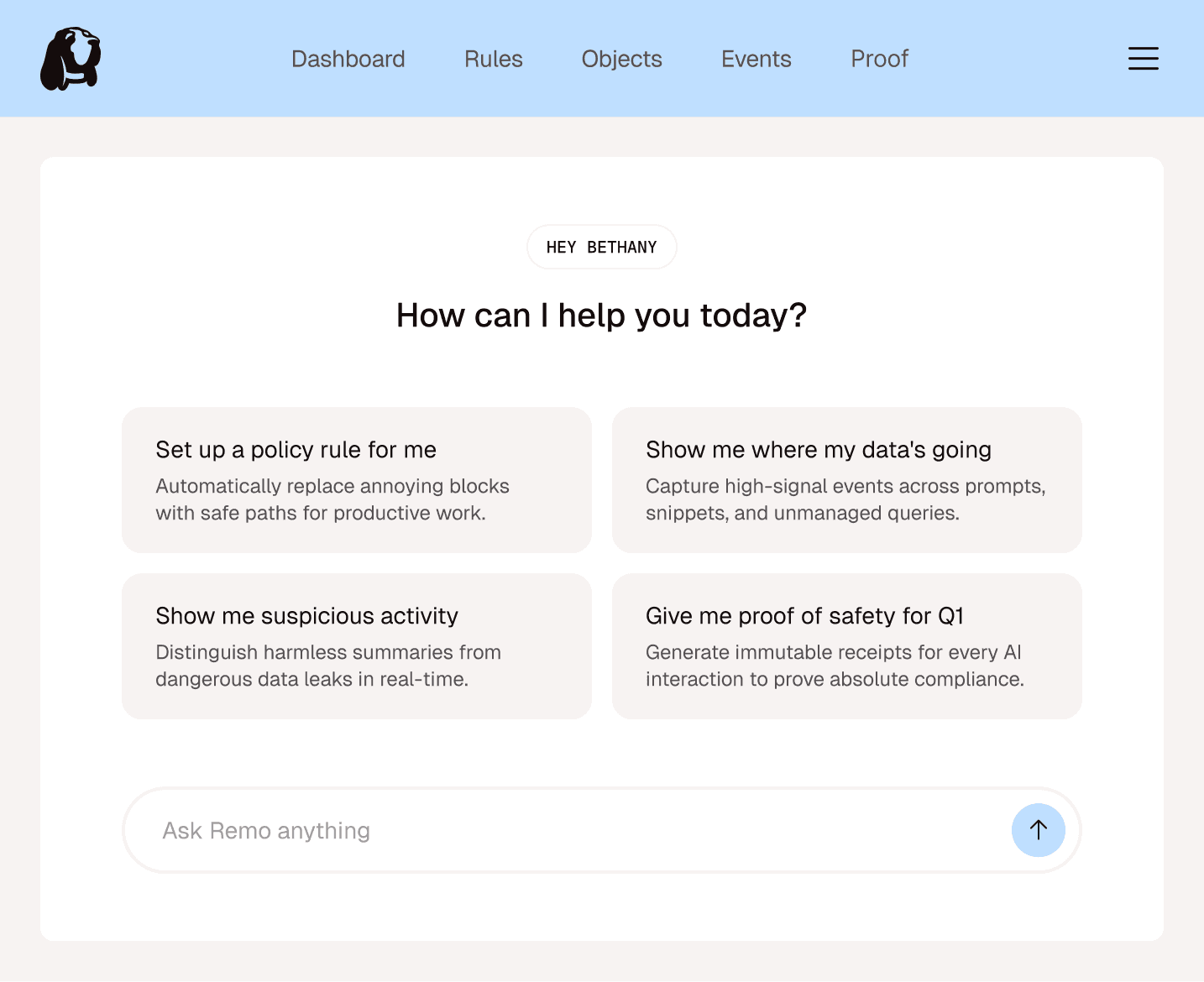
Meet Remo
Meet Remo
Meet Remo
Workflow security
for the AI era.
Workflow security
for the AI era.
Workflow security
for the AI era.
Preventing sensitive data from leaking into AI and modern workflows, without breaking how people work.
Preventing sensitive data from leaking into AI and modern workflows, without breaking how people work.
Built by experts in data security
and artificial intelligence
Built by experts in data security
and artificial intelligence
THE CHALLENGE
Security has been focused on protecting the wrong things in the wrong ways.
Security has been focused on protecting the wrong things in the wrong ways.
Security has been focused on protecting the wrong things in the wrong ways.
Humans work in flows, but security works in silos.
Humans work in flows, but security works in silos.
Traditional tools secure infrastructure checks but miss the dynamic data moving inside modern workflows.
When employees hit friction, they find workarounds.
When employees hit friction, they find workarounds.
When security blocks employees, they find workarounds in unmanaged apps to hit their deadlines.
These workarounds become massive, invisible liabilities.
These workarounds become massive, invisible liabilities.
Legacy tools have zero visibility into prompts and snippets, creating a massive, unmanaged $10M+ liability.
The Solution
Make your employee's existing behaviors and workflows safe by default.
01.
Interaction Control
We govern prompts, snippets, and queries—the new units of work.
02.
Workaround by Design
03.
Point-of-Decision Defense
04.
Immutable Proof
The Solution
Make your employee's existing behaviors and workflows safe by default.
Interaction Control
We govern prompts, snippets, and queries—the new units of work.
Workaround by Design
Point-of-Decision Defense
Immutable Proof
The Solution
Make your employee's existing behaviors and workflows safe by default.
Interaction Control
We govern prompts, snippets, and queries—the new units of work.
Workaround by Design
Point-of-Decision Defense
Immutable Proof
HOW IT WORKS
Remo turns invisible and risky workarounds into secure and safe productivity.
Remo turns invisible and risky workarounds into secure and safe productivity.
Remo turns invisible and risky workarounds into secure and safe productivity.
Carter needs some phone numbers reformatted quickly. As soon as Carter accesses an object, Remo becomes alert—capturing and observing the entire interaction.
Carter needs some phone numbers reformatted quickly. As soon as Carter accesses an object, Remo becomes alert—capturing and observing the entire interaction.
Carter needs some phone numbers reformatted quickly. As soon as Carter accesses an object, Remo becomes alert—capturing and observing the entire interaction.
integrations
Deploy anywhere. Integrate everywhere.
Deploy anywhere. Integrate everywhere.
Deploy anywhere. Integrate everywhere.


















and more!
and more!
and more!
WHY REMO
Workflow security built for human nature.
Workflow security built for human nature.
Workflow security built for human nature.
We secure the flow.
We secure the flow.
Legacy tools guard static files; we protect the dynamic sequence of work from start to finish.
We understand intent.
We understand intent.
Data logs are cold, but workflows tell a story. We distinguish harmless intent from dangerous leaks.
We empower employees.
We empower employees.
We replace the "silent block" with safe paths, guiding teams to sanctioned tools instead of the shadows.
We provide proof.
We provide proof.
Mistakes happen, but liability shouldn’t be a mystery. We generate verifiable receipts for absolute auditability.
THE INSPIRATION
Reimagining safety as a constant companion.
Reimagining safety as a constant companion.
Reimagining safety as a constant companion.
Remo is named after our founder’s dog, a loyal companion who stays on the trail no matter where it leads. We believe security should work the same way—not as a barrier that blocks your path, but as a guardian that follows your workflow. We built Remo to pick up the scent where traditional silos go cold, ensuring safety remains a constant companion through every interaction.
Remo is named after our founder’s dog, a loyal companion who stays on the trail no matter where it leads. We believe security should work the same way—not as a barrier that blocks your path, but as a guardian that follows your workflow.
We built Remo to pick up the scent where traditional silos go cold, ensuring safety remains a constant companion through every interaction.



COMMON QUESTIONS
How is this different than a DLP?
Traditional DLP tools miss what matters because they are blind to the shadow move. They can't see encrypted traffic or process-level context once data leaves a managed container. Remo is different because we operate at the system level. By using kernel, browser, and network sensors, we capture ground-truth visibility before encryption happens. This allows us to tie every action—like a copy-paste or a prompt—to the exact process and file involved, enabling far more accurate, real-time policy enforcement that doesn't break the user's workflow.
Does this break the employee's workflow?
No. Remo is designed to make the safe path the easiest path, replacing blocks with just-in-time coaching.
How do you handle audits?
Every decision generates an immutable receipt, proving exactly why an interaction was safe—perfect for deploying independently or integrating into your GRC platform.
Is it hard to deploy?
Every decision generates an immutable receipt, proving exactly why an interaction was safe—perfect for GRC platforms.
How is this different than a DLP?
Traditional DLP tools miss what matters because they are blind to the shadow move. They can't see encrypted traffic or process-level context once data leaves a managed container. Remo is different because we operate at the system level. By using kernel, browser, and network sensors, we capture ground-truth visibility before encryption happens. This allows us to tie every action—like a copy-paste or a prompt—to the exact process and file involved, enabling far more accurate, real-time policy enforcement that doesn't break the user's workflow.
Does this break the employee's workflow?
No. Remo is designed to make the safe path the easiest path, replacing blocks with just-in-time coaching.
How do you handle audits?
Every decision generates an immutable receipt, proving exactly why an interaction was safe—perfect for deploying independently or integrating into your GRC platform.
Is it hard to deploy?
Every decision generates an immutable receipt, proving exactly why an interaction was safe—perfect for GRC platforms.
book a demo
Secure the new units of work that legacy tools can’t see
Secure the new units of work
Turn annoying blocks into safe paths for your employees
Turn annoying blocks into safe paths
Get a verifiable receipt for every single interaction
Get a verifiable receipt for everything
It solves a big problem... being able to have holistic control and auditing over what people are doing—wherever they’re doing it.
CIO at $5B+ Regional Bank